10 Ways Hackers can hack your Account
Almost every one of us have social media(Facebook. Twitter, Linked-in) and mailing accounts (Gmail, Yahoo, Msn). The very thought of someone invading our privacy by compromising our account security and breaching in it is mind-devastating. In these article I will show you top 10 ways Hackers can hack your Account and how you can prevent yourself by using some simple cyber-hygiene.
-
Phishing:
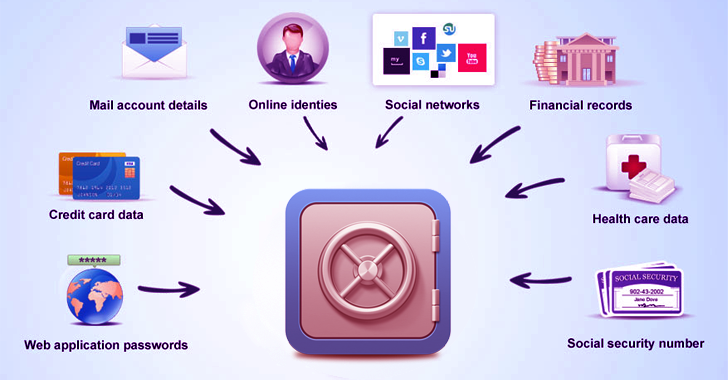
Phishing is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and indirectly money), often for malicious reasons, by disguising as a trustworthy entity in an electronic communication.
Attacker usually creates a fake website which has the look and feel which are almost identical to the legitimate one. Like www.facebok.com (notice there is single ‘o’ in Facebook) instead of www.facebook.com. And then tries to acquire personal information such as password from you. It is typically carried out by email spoofing or instant messaging, and it often directs users to enter personal information at a fake website

ADVICE: Make it a practice to visit websites by entering their specific URL’s in the address bar yourself and not by clicking the links in some mails or messages. One Wrong Click can cost you alott!
-
Keylogging:
Keylogging is the easiest way to hack a account. Keyloggers are sometimes so dangerous that even people with good knowledge of computers can fall for it. Basically, Keylogger is a small program which once installed on a victim’s computer will record everything which the victim types on his/her computer. The records are then sent to the hacker directly on his email address.
ADVICE:
- Use a Firewall: Keyloggers send the information from victim’s computer through the internet, so a firewall will monitor your online security and block out anything suspicious
- Password Manager: Keyloggers can’t steal what you don’t type, Password Manager fills out important forms without you having to type it.
Password Manager
-
Stealers:
One thing that even most of professionals do is that they keep complex passwords but then don’t want to remember those complex passwords so they make their browser remember them. The Browser automatically fills in the password field for you when you visit the site. Now to fill the passwords automatically browsers need to store the passwords locally in computer. Stealers are softwares made to fetch those saved passwords from the browsers.
ADVICE:
- Use Password Managers
- Avoid saving passwords on browsers

-
Session Hijacking:
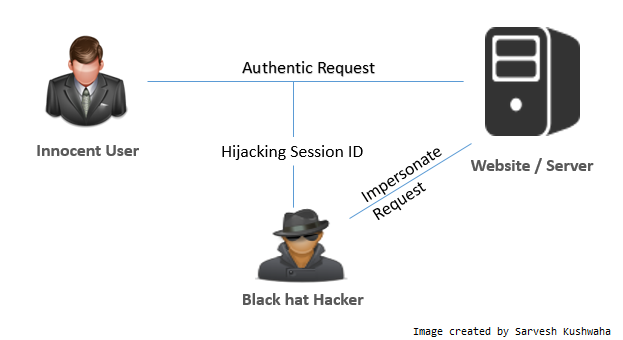
Session Hijacking can be often very dangerous if you are accessing a website by a http:// connection. In a Session Hijacking a hacker steals the victim’s browser cookie, which is used to authenticate a user on a website and uses it to access victim’s account. Session Hijacking is mostly done on LAN network.
ADVICE:
If you use chrome, then install an add-on called KB SSL Enforcer. OR if you firefox then install Force TLS. These add-ons will automatically redirect you to the secured pages of the websites
-
Side Jacking / Firesheep:
Side Jacking is a popular method for hacking accounts. It is a process of stealing someone’s access to a website on a wireless public networks.
Firesheep is used to carry out side jacking when attacker and victim are connected to same Wi-Fi network. Side Jacking is just another name for session hijacking but precisely targeted for Wi-Fi users.
ADVICE:
- If you use chrome, then install an add-on called KB SSL Enforcer. OR if you firefox then install Force TLS. These add-ons will automatically redirect you to the secured pages of the websites.
- Avoid Connecting to open public wireless networks.

-
Mobile Phone Hacking:
Millions of user access their mails and social media accounts through their mobile devices but if your smartphone is compromised. Your phone has a lot of your personal data apart from your selfies. It has your email account which can be used to reset the passwords of your social media accounts and bank accounts. Moreover, smartphones nowadays are open to attack 24 hours a day, seven days a week with only minimal security in them thus making them a suitable target for hackers.
Click here to know how to prevent your smartphone from getting hacked.

-
Usb Hacking:
If an attacker has direct access to your laptop or personal computer, he can insert a usb stick specially programmed to extract saved passwords and login credentials.
ADVICE:
- Don’t leave your laptop unattended.
- Install softwares that tells your computer not to accept unrecognized devices.

-
Man in the Middle Attack:
If the attacker and victim are on same network, then the attacker can place himself between the client and the server or he could also act as a default gateway and capture all the traffic in between.

-
Botnets:
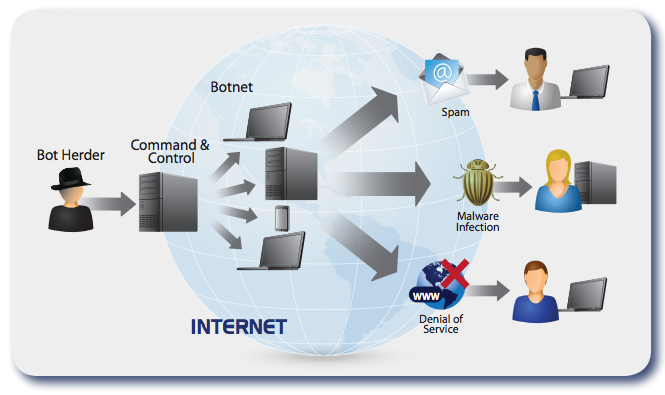
Botnets are not commonly used for hacking social accounts because of its high setup cost. A botnet is basically a collection of already compromised computers. The infection is same as keylogging, however a botnet gives you additional options for carrying out attacks with compromised computer.
-
DNS spoofing:
Again this attack is possible when both the attacker and victim are on same network. The attacker can use DNS Spoofing by changing the original facebook.com page to his own fake facebok.com page and get access to victims Facebook account.
Tips to Avoid being a victim:
- Change Password: Change password of all your accounts every 3 months.
- Avoid “remember password”.
- Size Matters: Your Password should be of 12 characters with numbers, characters & letters. Cracking a 12-digit password will take on an average 2 years.
- Login Alerts: Facebook and gmail can send you an alert everytime someone logs into your account from new device or browser.
- Enable 2-Step Verification.
- On social Media, do not accept friend requests from people you don’t know. Scammers create fake accounts & friend people. Once they have friended you they can spam your timeline, tag you in inappropriate posts, send you malicious messages and even target your friends.
Found it Interesting? Got Something to ask??
Feel free to comment it below.
Stay Secure ! Stay Happy !!




