PDoS – A Permanent Denial of Service
Imagine a fast moving bot attack that is not designed for collecting data, but instead, is used to deny a victim’s technology from functioning at all. That’s crazy right? Well, not really. PDoS has been around for a long time; however, it only shows itself to the public from time to time and right now in 2017 is gaining a lot of attention. First let’s get our basics revised by understanding what is denial of service (DOS).
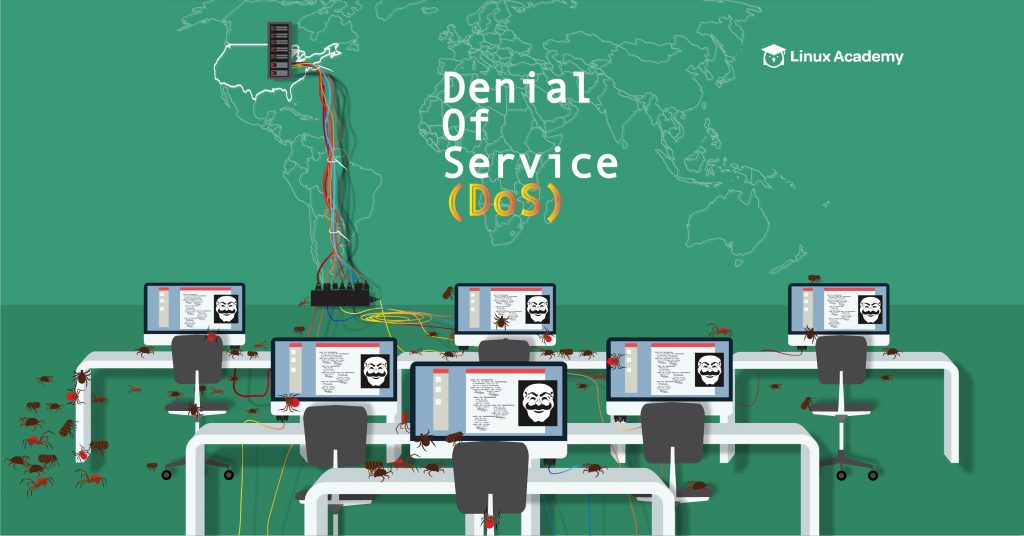
What is DOS Attack?
Denial-of-service (DoS) attacks typically flood servers, systems or networks with traffic in order to overwhelm the victim resources and make it difficult or impossible for legitimate users to use them. While an attack that crashes a server can often be dealt with successfully by simply rebooting the system, flooding attacks can be more difficult to recover from.
What is PDOS Attack?
Permanent denial-of-service (PDoS), also known loosely as “phlashing” is an attack that damages a system so badly that it requires replacement or re-installation of hardware.
Unlike its brother distributed denial-of-service attack(DDoS), a PDoS attack exploits security flaws which allow remote administration on the victim’s hardware. After which the attacker can completely destroy hardware devices such as routers, printers, or other networking hardware. The attacker uses these vulnerabilities to replace a device’s firmware with a modified, corrupt, or defective firmware image (a process which when done legitimately is known as flashing). This therefore “bricks” the device, rendering it unusable for its original purpose until it can be repaired or replaced.
A PDoS attack would result in a costly recovery for the victim, since it would mean installing new hardware. At the same time, it would cost the attacker much less than a DDoS attack.
The PDoS is a pure hardware targeted attack which can be much faster and requires fewer resources than using a botnet or a root/vserver in a DDoS attack. Because of these features, and the potential and high probability of security exploits, this technique has come to the attention of numerous hacking communities.
Some related recent articles on PDos :
1 ) New “Brickerbot” malware attacks insecure Wi-Fi networks and smart home gadgets.
2) Beware of ‘BrickerBot’, the Destroyer of Unsecure Internet Devices – Homeland Security.
Source: Wikipedia
Found it Interesting? Got Something to ask??
Feel free to comment it below.
Stay Secure ! Stay Happy !!




